Last updated on March 15th, 2023 at 02:49 pm
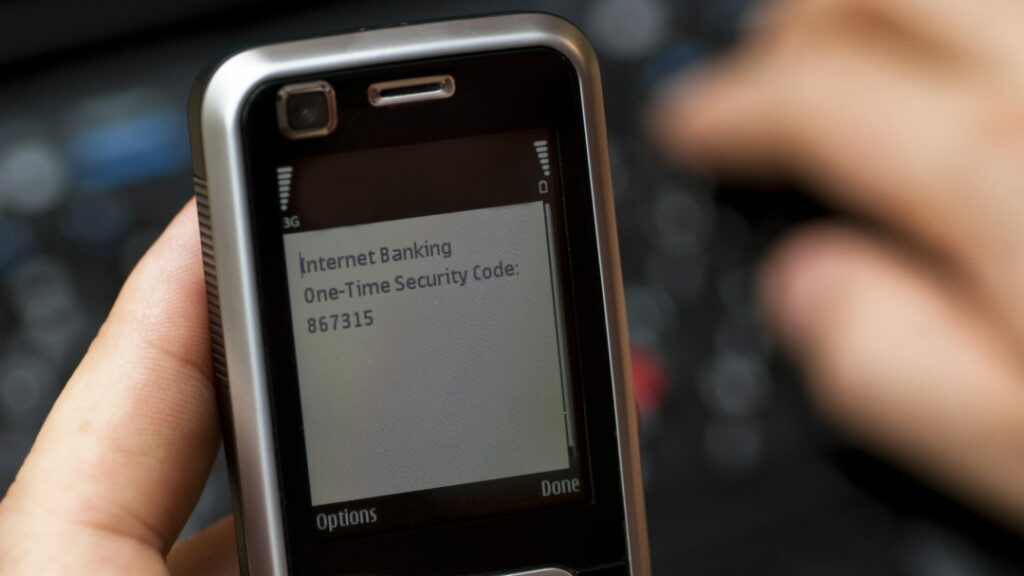
In the previous post, we saw SMS is the most popular form of two-factor authentication (2FA). But while SMS-based 2FA offers much more protection than just a password alone, you should switch to an alternative form of 2FA if possible. Here’s why:
Reason # 1: SMS-based 2FA is not secure

If you use SMS-based 2FA, you’re vulnerable to SIM-swapping attacks.
In a SIM-swap, cybercriminals steal your phone number, meaning they get all of your texts, including any 2FA codes sent to you. If they have your password, e.g. from a data breach or phishing, they now have everything they need to break into your account.
Worse, some accounts allow you to reset your password via SMS, meaning hackers don’t even need to know your password to take over these accounts if they target you with a SIM swap.
Reason # 2: You might not always be able to receive texts

If you travel abroad, you might find yourself without cell phone service. And while many carriers and smartphones now offer Wi-Fi-calling, allowing you to receive calls and texts so long as you’re connected to Wi-Fi, not all do.
This means that if you go on vacation or travel for work, you might be unable to receive your 2FA codes when you need them. So, unless you have a backup code with you, you’ll be locked out of your accounts until you return home.
Reason # 3: Companies may abuse your phone number

To use SMS-based 2FA, you have to hand over your phone number. Unfortunately, this gives companies the opportunity to use your phone number in ways you probably don’t want.
For example, both Facebook and Twitter have been caught using the phone number you give them for SMS-based 2FA to target you with ads. In other words, advertisers said “I want to show this ad to people with these phone numbers,” and Facebook and Twitter complied, using the phone number you gave them for 2FA to determine whether that ad showed up in your feed. Not cool!
Reason # 4: Your phone number could end up in a data breach

Even if a company doesn’t use your phone number in ways you don’t expect or want, it could still get hacked, exposing your digits to cybercriminals.
The hackers could then use your phone number to target you with a SIM-swap. Or they could sell your information to other cybercriminals, leading to all kinds of annoying and potentially dangerous scam texts and calls.
Alternatives to SMS-based 2FA
If you’ve decided to move away from SMS-based 2FA, what should you use instead? Here we’ll look at two good options: authenticators and security keys.
First, though, a caveat. Not all online services offer anything beyond SMS-based 2FA. For those accounts, then, you’re stuck with SMS. You could reach out to the service provider and ask them to consider adding alternative 2FA options, but SMS-based 2FA still offers far more protection than no 2FA at all.
Fortunately, though, many online services offer authenticator based 2FA and more and more are offering security keys.
Option 1: Authenticator apps

An authenticator app, like Authy, Google Authenticator or Microsoft Authenticator, is a solid alternative to SMS-based 2FA. These apps generate codes on your smartphone that you enter as part of the login process, just like the codes you receive via text. But authenticators avoid many of the problems that afflict SMS-based 2FA.
Unlike SMS-based 2FA, authenticator apps are not susceptible to SIM-swaps. They also work even if you’re completely offline, so you don’t have to worry about being locked out of your accounts while traveling. Plus, most authenticator apps don’t ask you to give up your phone number (Authy is an exception), making them a more private option compared to SMS-based 2FA.
However, you’ll need to back up your authenticator to avoid getting locked out of your accounts if you lose or upgrade your phone.
Authy makes this easy with cloud backup and multi-device sync. This means you can install it on your phone, tablet and even your laptop, and any changes you make on one will automatically show up on the others as well.
Microsoft Authenticator also offers cloud backup, though not multi-device sync. However, it has a big limitation: You can’t restore a backup across platforms, meaning you’re out of luck if you’re moving from an Android phone to an iPhone or vice versa.
Surprisingly, Google Authenticator doesn’t offer any cloud backup or multi-device sync capabilities. However, you can back up your authenticator data manually via the export accounts function.
Option 2: Security keys

While authenticator apps are a good option, a hardware security key, like a Yubikey, provides the most secure form of 2FA.
Security keys are USB-like devices you plug into your laptop or phone to confirm your identity. They offer protection against advanced phishing techniques that SMS and authenticator based 2FA have little defense against. That’s because a security key knows whether the URL of the site you are trying to log in to is correct and won’t authenticate on an imposter site.
Security keys also work offline and won’t ask you to hand over your phone number.
Unfortunately, security keys aren’t yet supported by all services. They’re also not free. The cheapest Yubikey costs around $25, but as it’s a good idea to get a backup, realistically you’re looking at spending $50.
The takeaway
From a security, privacy, and availability standpoint, SMS-based 2FA is not a great choice. Fortunately, most services offer alternatives. Check them out and see which works best for you!
