Last updated on March 9th, 2023 at 03:59 pm
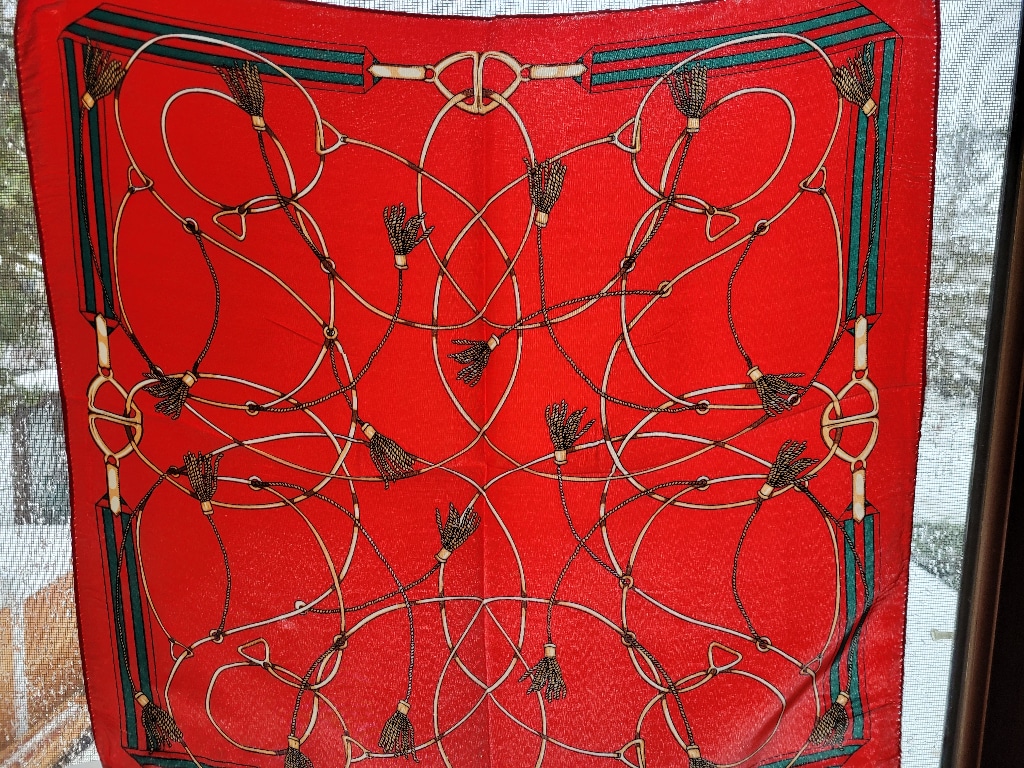
About a month ago, my husband, Erich, received an Amazon package he didn’t order. Inside was a low-quality red scarf patterned with gold tassels. I assumed a friend had sent it as a gag gift and quickly forgot about it.
Ten days later, another unordered Amazon package arrived. When Erich opened it, he found the same ugly red scarf inside. I then realized this hadn’t been sent as a gift, but was part of a scam.
The most expensive ugly scarf ever?
When Erich checked his Amazon account, he found it had been hacked. His order history showed cybercriminals used his credit card to order both scarves and have them shipped to our address.
However, sneakier hackers archive the orders they place so they don’t show up in the regular “Orders” section of your Amazon account. Instead, they end up hidden in the “archived orders” list, so check there as well if you think someone has access to your account.
You might think we got off pretty easily since the criminals only used Erich’s credit card to order two ugly scarves. After all, the unauthorized charges would be small, right?
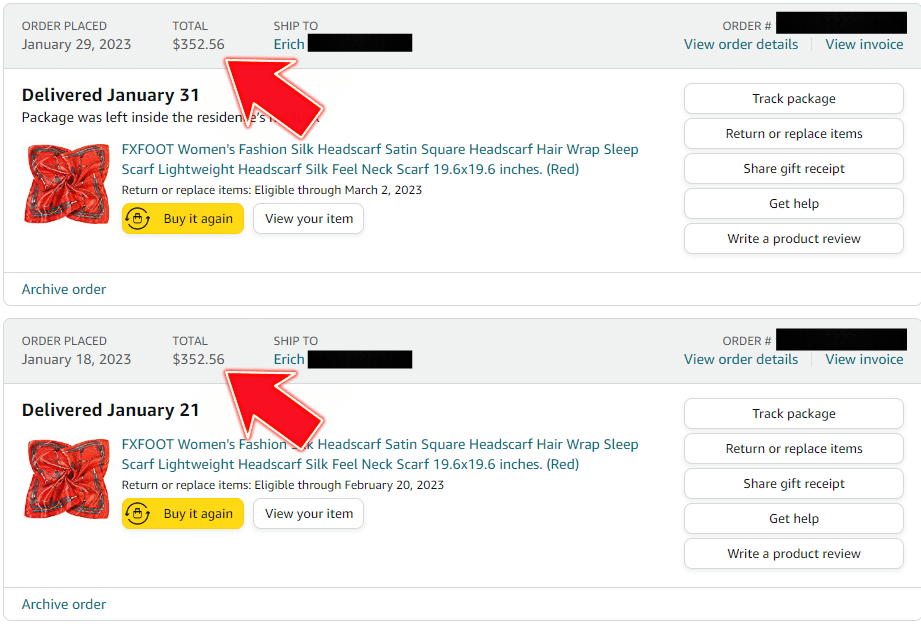
Unfortunately not. Each scarf cost an eye-popping $352.56, meaning Erich was fraudulently charged $705.12 in total.
Curious about the bizarrely overpriced scarves, I searched for the brand that made them and found 31 similar ones for sale on Amazon. However, the prices had been hiked, and they were listed at $499 each.
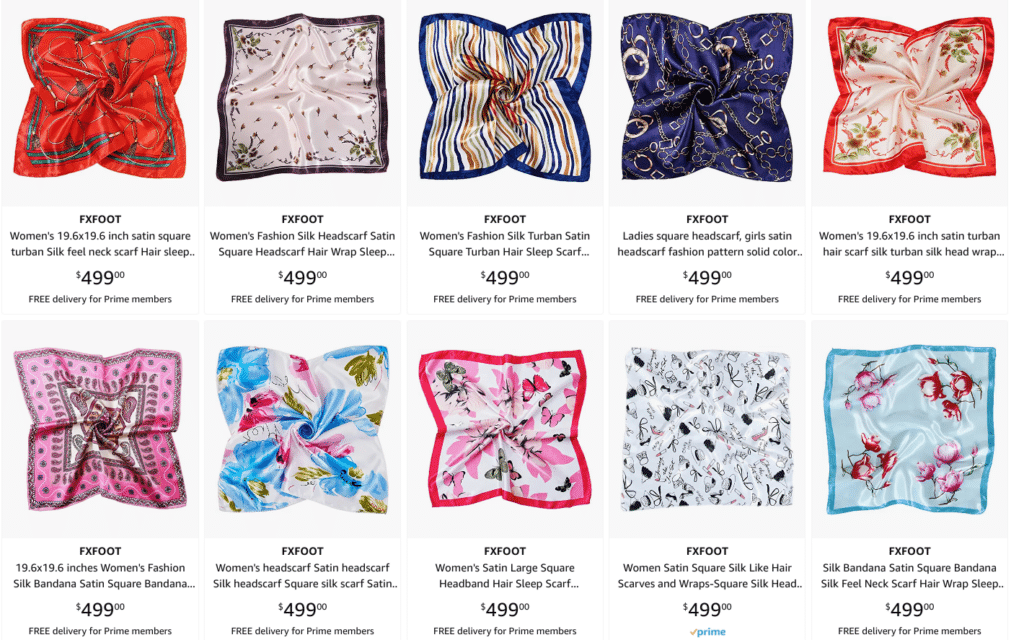
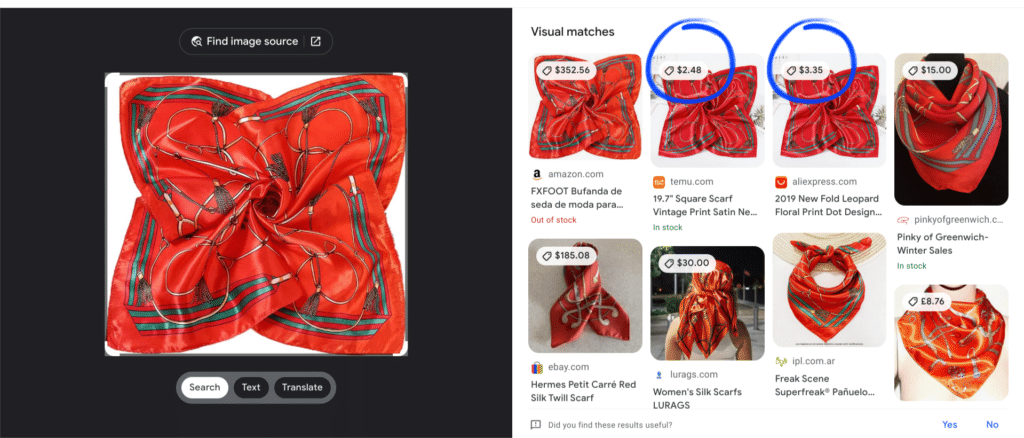
I also did a Google Lens search for the image of the scarf Erich received. This revealed the same scarf was available for purchase on Temu and AliExpress for the much more realistic price of $2.48 and $3.35, respectively.
Based on what happened to my husband, I think these scarves are part of a scam I’ll call the “ugly scarf scam.” Here’s how I’m guessing it works:
- Shady Amazon sellers list cheap, low-quality items for sale at ridiculously high prices.
- The sellers use hacked accounts (or fake accounts with stolen credit cards) to buy these overpriced items.
- They then ship the shoddy goods to the victim’s address to make everything seem legitimate to Amazon.
As the items are cheap but sold for hundreds of dollars each, the sellers make a tidy profit from this nasty scheme.
How we secured my husband’s account
After we realized Erich’s Amazon account had been hacked, the first thing we did was change his password. I set him up with 1Password last year, so we used its password generator to make a strong, unique password for his account.

Next we enabled two factor authentication (2FA) using Authy. That way, even if Erich’s password gets leaked in the future, hackers won’t be able to get into his account without also entering a code from the app, which should be difficult, though not impossible, for them to get.
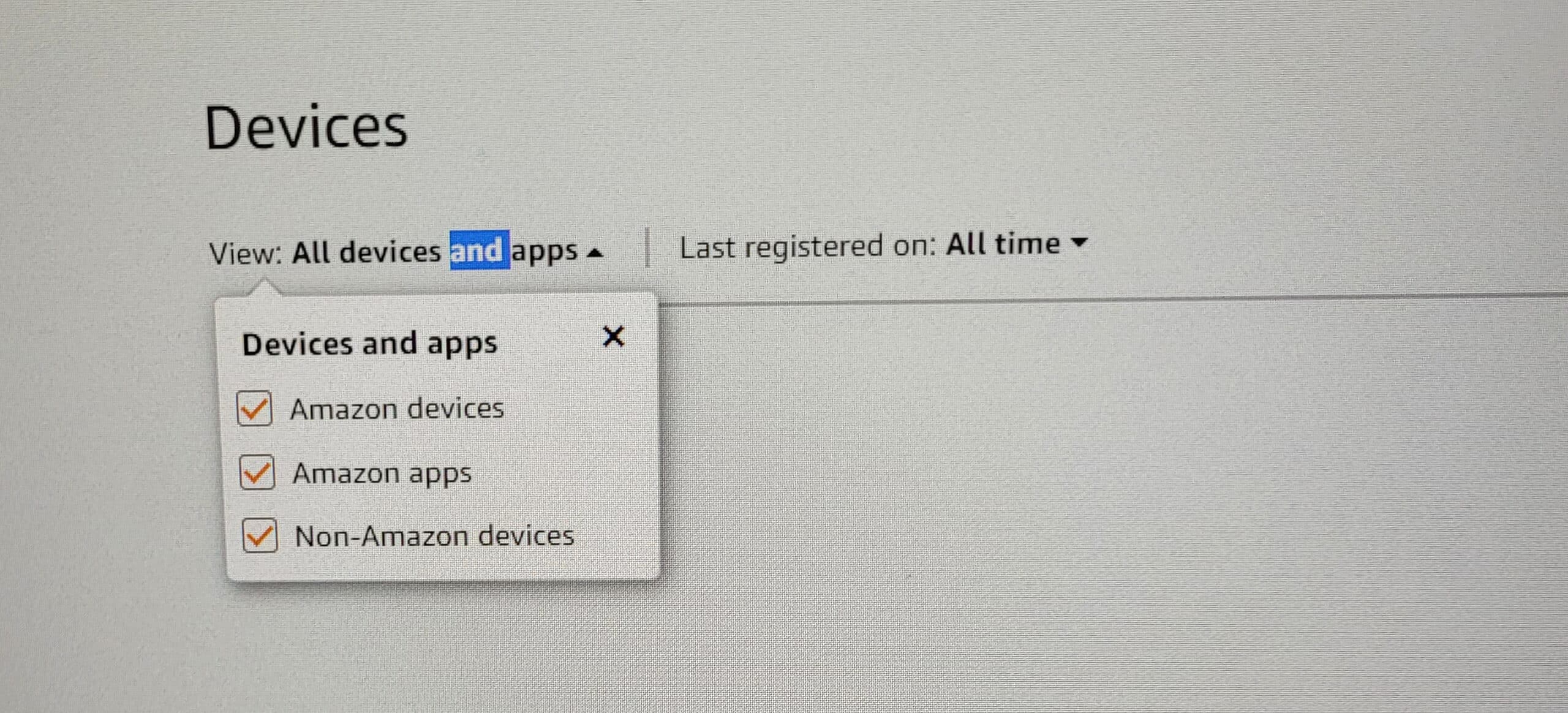
We then checked for any unrecognized devices and apps that had access to his Amazon account. We did this by going to his account page, scrolling down to “Digital content and devices” and selecting “Manage content and devices.” We then navigated to the “Device” tab and confirmed that there were no suspicious devices or apps with access to his account.
Next we scanned Erich’s computer for malware, just in case there was anything nasty stealing his passwords, logging his keystrokes or nabbing screenshots. Fortunately, that came back clean. If the scan had found something suspicious, however, we would have had to change his Amazon password again and reset his 2FA to make sure the malware wasn’t sending the scammers information they could use to get back into his account.
Then we changed the password on Erich’s other accounts that used the same password he had used for his Amazon account. We also checked for any unusual activity in those accounts, because the scammers could have gained access to those as well. Fortunately, everything seemed normal. He also set up 2FA on those accounts for maximum security.
Finally, Erich contacted Amazon’s support team to request a refund for the fraudulent charges and to report the scam. While the customer service agent was polite and said Amazon would refund the cost of the scarves, they said nothing about our request to report the scam.
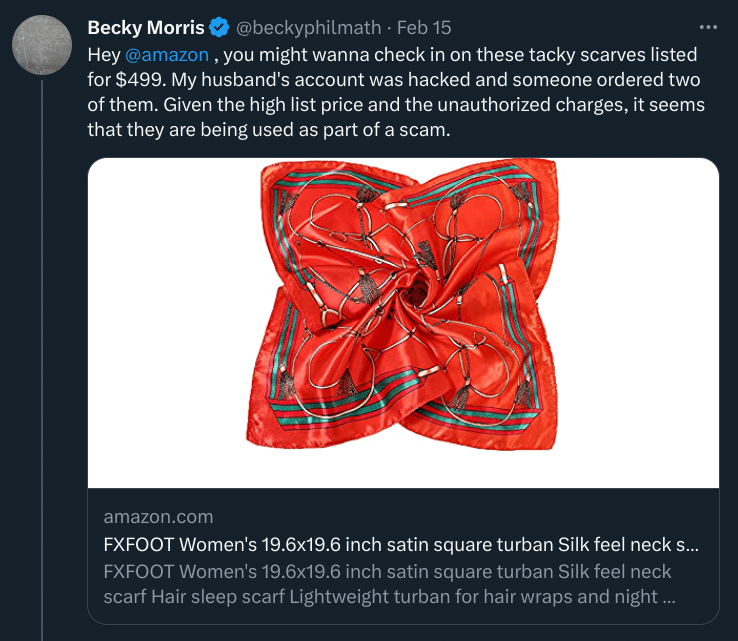
I also reached out to Amazon on Twitter to alert them to the potential scam. But, as of the time of writing, the scarves remain listed on Amazon for $499.
How my husband’s account was hacked
After we secured Erich’s Amazon account, I checked both the email associated with it and his old password over at haveibeenpwned.com to see if they had been leaked in any data breaches. Sure enough, his email address and password were part of 12 breaches. Oof!
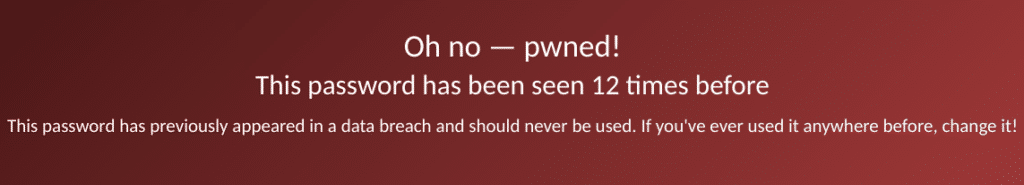
This meant Erich’s Amazon account was likely hacked by credential stuffers. Credential stuffers take usernames and passwords leaked in data breaches at one company and use them to try to log in to other websites. So the hackers may have found Erich’s email and password from one of the 12 breaches it was leaked in and hit the jackpot when they used them to try to log in to his Amazon account.
That’s why security professionals tell you to never reuse your password!
The takeaway
If you receive packages from Amazon you weren’t expecting, check your account right away to see if there are any fraudulent orders. And while you’re there, take the time to set a strong, unique password and enable 2FA for maximum protection.
Update March 9th
Unfortunately, the above security measures were not sufficient to lock down Erich’s account. Just a few days ago, hackers placed an order for a low-quality but ridiculously priced tie as well as, rather oddly, a regularly priced underwear set. This time, they had also been more sneaky and had hidden the order by archiving it.
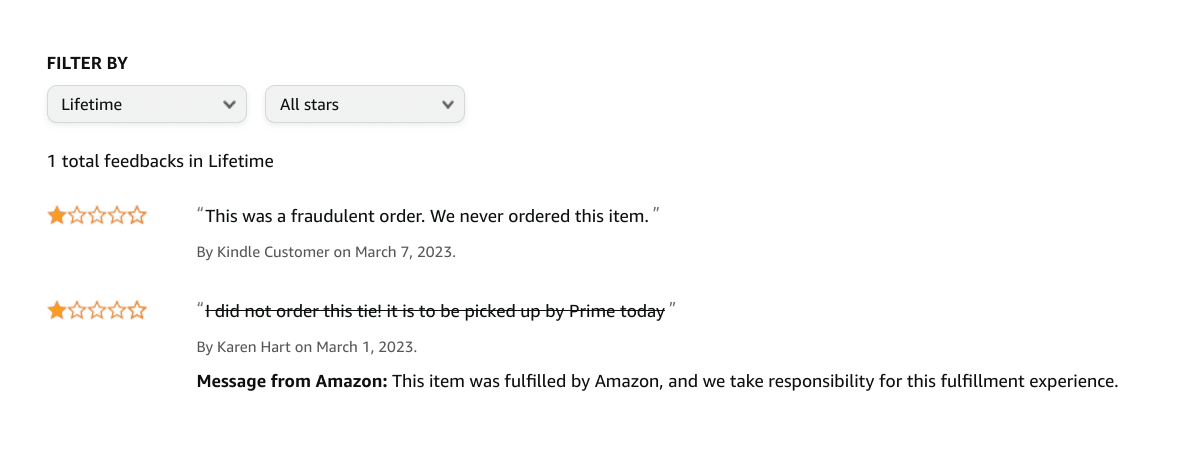
Judging by the tie-seller’s Amazon reviews, other people had been receiving fraudulently ordered items as well.
Given we had changed Erich’s password and set up 2FA, how could this happen? It seemed to me there were two options: 1) Erich’s PC was infected with malware, despite the previous scan coming back clean; 2) The hackers had added an app or device to Erich’s account that did not show up in the “devices” page and had not had its access revoked when we changed his password and added 2FA. While option 2 sounds far-fetched, similar situations have been reported previously.
To check for malware, we ran a more thorough scan. However, again, everything came back clean. That left a device or app that, despite not showing up in Erich’s account, somehow still had access.
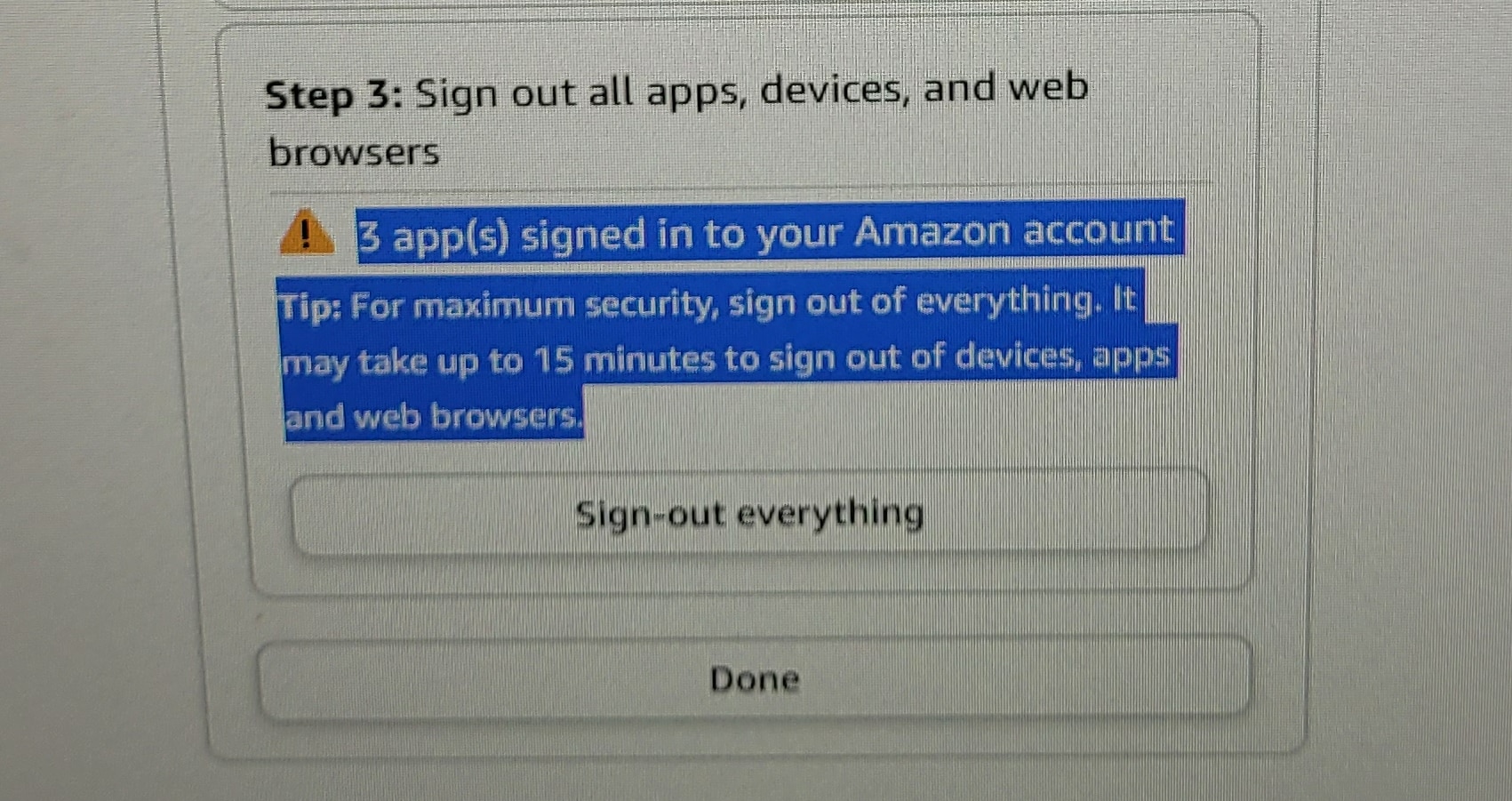
To revoke access to any phantom apps or devices, we went to “Login and security” and selected the “Compromised account” option. We scrolled down to the “Sign-out everywhere” button, where we saw a warning that three apps had access to Erich’s account, even though zero were listed on the “devices” page of his account. This may well have been the hacker’s point of entry! We then revoked their access, hopefully kicking the hackers out, and changed Erich’s password again for good measure.
Fingers crossed that keeps the hackers out for good this time!

Thank you for letting us know about this scam and cant believe they were able to archive the order. Its great to know that you are on their case and not only alert us to the scam but also show us how to make sure our computer is safe afterwards.